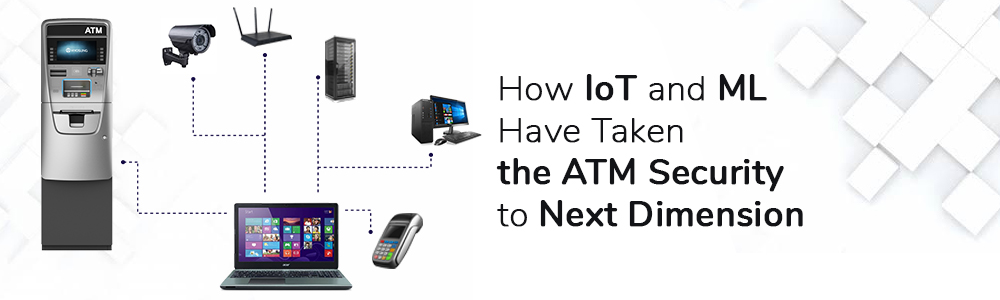
Using the Internet of Things and Machine Learning to protect banks and ATM sites is the latest trend in the banking and finance field. In addition, different IoT-based devices can help to reduce the increasing operating costs of ATMs and increase their performance.
This innovation is rapidly catching up with various banks in India in the private and government sector. Now ATM systems become more complicated and serve a variety of security functions turning criminals, robbers, and hackers into high-priority targets.
High safety protection measures enforce trendy ATM machines. They function for transactions under advanced systems and networks. Often encrypted the data stored by the ATMs area unit, but hackers will use covert hacking tools to access accounts and remove the account balance.
As an alternative, unskilled robbers are trying to steal their withdrawn cash or account from bank patrons with a gun.
The ATM machines are launched, built, and distributed to a large percentage of our society and withdraw cash using the debit & credit cards. In contrast, card fraud and illicit access became a very serious threat to both the financial sector and individuals.
The ATM-related robbery dependent on unauthorized access has also dramatically increased in recent years. There was a rising proportion of about 90 percent among the robbery in the financial sectors. The ATM, which is theft, is only discovered after the robbery has been completed or the amount has been debited from the registered user’s account.
Now we do not need to worry because Machine Learning (ML) Development and IoT are combined together to solve all these kinds of problems because IoT and Machine Learning-based ATM security provide tight security to all ATMs.
The raspberry pi 3 is mainly used in this IOT project as the part that holds in it the Face Detection Cascade used for face detection and face recognition Local Binary Patterns algorithm. The camera is used to track the user’s correct images.
RFID Reader is used as a reader for the ATM card. TAG is the ATM card used. As the electrical switch, the relay is used. The OTP and the warning message are sent to the user via the standard SMPP message protocol where the code is written in the python language and loaded in the pi3 raspberry.
Therefore, this new technique deals with the method of preventing ATM robbery related to unauthorized users by allowing access to the user only after the user identity has been checked using the user image taken via the CCTV camera installed on the ATM and face detection using the face hair cascade, face detection using the
Local Binary Pattern algorithm. If the OTP entered in the ATM by the user is incorrect, the warning message will be sent immediately to the authorized user. Keep reading to understand why IoT and ML software is exactly helping banks’ ATM centers.
Demand Forecasting Methods: Using Machine Learning to See the Future of Sales
What is the Internet Of Things (IoT) All About?
The Internet of Things (IoT) is a collection of interrelated computing devices, mechanical or virtual machines, objects, animals and individuals with unique identifiers and the ability to transfer information over a network in the absence of human-to-computer or human-to-human communication.
Simply put, the Internet of Things is about linking devices that are internet-enabled to relay information back to us, cloud-based apps, and one another (device to device).
Including mobile phones, fridges, washing machines and wearable’s, medical equipment, and jet engines, these’ smart’ devices can be anything. Essentially, artifacts use the network and unique identifiers like RFID tags or processors to function as part of the internet in the Internet of Things.
The Internet of Things (IoT) Development has been rapid and successful in today’s technology world. As the IoT initiatives are applied both in government and in the private sectors of our society.
Role of IoT Providing Security
IoT security is an area of effort to protect connected devices and networks on the Internet of Things (IoT). The Internet of Things includes the increasing prevalence of objects and entities–defined in this sense as things that have unique identifiers and the ability to transfer data automatically over a network.
Much of the rise in IoT connectivity comes from mobile phones, embedded sensor systems used in machine-to-machine (M2 M) communication applications, and wearable computing devices.
The main problem is that due to the relatively new idea of networking appliances and other objects, security was not always considered in product design. IoT products are often sold with embedded operating systems and software that are old and unpatched.
In contrast, consumers often fail to change the default passwords on smart devices— or fail to pick powerful enough passwords when they change them. An IoT system that needs to be directly accessible over the Internet should be segmented into its own network and have limited access to the network to improve security.
In order to identify possible anomalous traffic, the network segment should be monitored and action should be taken if there is a problem. Since the IoT definition was first suggested in the late 1990s, security experts have advised about the great potential risk of large numbers of unsecured devices connecting to the Internet.
A researcher at Proof Point, a business security firm, discovered the first IoT botnet in December 2013. More than 25% of the botnet consisted of devices other than computers, including smart TVs, baby monitors, and other household appliances, according to Proof Point.
Let Us Check Out Some of the Benefits of ATM
- Save time
Maybe that is the most profit. Save time driving down to the store and you, do not have to wait in the queue to do your transactions. For various transactions listed above, the ATM Card facilities provide you with instant banking options.
- Convenient 24×7 Banking
You are not bound to do your transactions during banking hours at the ATM now. There is no need to be concerned about bank holidays or public holidays. It is a banking facility available 24x 7, 365 days a year.
- Withdraw Cash When Overseas
Depending on the type of facility that your bank offers, if you are traveling overseas, you can use the card to draw currency from the ATM in the country you are traveling to. Of course, if your bank has given you this service, you must check in advance.
- Universally Accepted
You may forget to carry loads of cash with you, whether you’re in town or out of town (or in another country). Only bring your debit card with your ATM cum and everywhere it is normally accepted.
However, if they have a program to accept credit and debit cards, you have to check with the restaurant or hotel. If there is a MasterCard icon on your debit card, you can be almost certain. You should also make sure that you tell your bank that you are leaving your station and that the service should be interrupted.
- Security Features
ATM use is limited to the person who knows the PIN only. Therefore, if you keep the secret PIN then except you no one can use it to do the banking transactions using the ATM.
You can also set daily transaction limits for security purposes, and ATM receipts can help you track your transactions and withdraw or transfer money. As an additional security measure, you can also switch your PIN.
- Save Your Account from Being Dormant
Often one or the other account will be dormant if you have not made a transaction for about 6 months. It is a problem to make it operational again.
The explanation for this is that most of us have tough time constraints. Today, at regular intervals, you can do one small transaction to keep it going.
- Helpful Budgeting Tool
You can never go overboard with your money expenditure with an ATM debit card. The debit card guarantees that only the amount of money you have in your bank account can be spent.
This means you cannot go into a “credit card debt” scenario. Unlike credit cards, this helps you to remain strictly within budget limits.
Machine Learning With IoT Components Used To Secure
Here we present the IoT components used for ATM security using the Machine Learning technique.
- Raspberry Pi 3
The raspberry pi 3 is a mini-computer and user-friendly with a very solid model. The raspberry pi 3 holds the operating system, and programs for the compilation and running of a project also hold the documents.in our project, the raspberry pi 3 is used to store the code for face detection, face recognition, and for the alert message module with other IoT components.
- RFID (Reader and TAG)
- RFID (Radio Frequency Identification) Reader
The RFID reader is used to track the tag, which includes the account data of the user.
- RFID (Radio Frequency Identification) Tag
The RFID tag is used to store the user account information by using the RFID reader to detect the respected information in the database.
- Resister
Resister is mainly used to control current flow in terminated transmission lines of electronic circuits, increase current flow, and divide voltages, change signal levels.
- DPDT Relay
DPDT (double pole double throw relay) is used to link the input from two outputs to the same output of one.
- Transistor (BC 547) – DC Motor (12 volts)
The transistor is a device with a semiconductor that is used to control the current flow through its one terminal.
- CCTV Camera (25 MP)
The 25 MP cameras are used to get the user’s photos that reach the atm.
- DC Motor (12 volts)
The DC motor is the machine used to transform electrical energy into mechanical energy. If the user specifics are right or the OTP entered is correct, the DC MOTOR used in our project to rotate.
Result After Implementing the IoT Technique
We implemented the IoT model using suitable components with the raspberry pi 3. First, when issuing the debit or credit card, the user is subjected to photography from different angles.
The images taken are stored and converted to grayscale images to reduce errors while the user’s grayscale image is divided into many pieces and each piece is given a value and stored.
One of the elements that are cameras used to detect the face of the person approaching the ATM by using the face-detection haar cascade, which is a qualified XML file when holding the XML code to detect a person’s face of any gender and collecting the image of the face of the users approaching the ATM machine.
The user’s accrued images have also transformed into a grayscale images and divided into different pieces and values. Based on the data contained in the user’s card, the values of the identity of the approaching user have been compared to the valued values of the user’s image that were processed and registered during the process of issuing the card.
Areas Where This Technique Can Be Implement
- Can be applied for many government purposes
- Can be used in different fields for security purposes
- For more security purposes, some more modules can be included
Conclusion and Future Scope
Thus the IoT technique using the raspberry pi and its components with some face detection Haar cascade is detected and recognized if found incorrect then the OTP is sent to the user, if the approaching user enters the wrong OTP then the error message is sent to the user as a text message.
It is evident from the system proposed above that different techniques are necessary to stop ATM robbery. We have suggested different approaches to ATM control and safety through different studies. It reduces costs with this revolutionary approach and improves the efficacy of ATM security.